News & Updates
The latest news and updates from companies in the WLTH portfolio.
Biggest IPO ever? SpaceX buzz ignites rally talk in top cryptocurrencies - what to know
Singer D4vd faces death penalty for murdering and dismembering body of 14-year-old girl Celeste RivasSpaceX IPO impact on Bitcoin: The buzz around a potential SpaceX initial public offering (IPO) is building quickly, with expectations that it could become the biggest IPO in history, as per a report. As attention grows, investors are not only looking at SpaceX stock exposure but also at how a listing could ripple through the broader crypto market. SpaceX currently holds over $600 million in Bitcoin (BTC) on its balance sheet, making it the fourth-largest corporate holder of Bitcoin globally, with 8,285 BTC, as per The Motley Fool report. This has already placed the company among notable corporate crypto holders, alongside firms like Block, which holds 8,883 BTC. The size of SpaceX's Bitcoin position is drawing attention because it could set a precedent for other major tech companies. If a company of its scale were to expand its use of Bitcoin as a treasury asset, it may encourage broader adoption across the tech sector. Some market observers suggest that a SpaceX valuation potentially reaching $1.75 trillion could amplify this effect. The idea is that if large tech firms begin following similar strategies, Bitcoin could see stronger long-term demand driven by corporate balance sheets, as per The Motley Fool. Beyond Bitcoin, Dogecoin (DOGE) is also being discussed in relation to SpaceX. Elon Musk has previously supported DOGE publicly and even suggested ideas such as it becoming a future interplanetary currency or being used for moon missions, as per The Motley Fool report. This has fueled speculation that renewed attention around SpaceX could also bring interest back to the meme coin. At the same time, concerns remain around scam tokens. A coin named SpaceXCoin has already appeared and reached a $100,000 market cap, as reported by The Motley Fool. However, it is noted that there is currently no official SpaceX crypto token, and such projects are typically associated with pump-and-dump risks. How much Bitcoin does SpaceX own? SpaceX holds 8,285 BTC on its balance sheet. Are there official SpaceX crypto tokens? No, there is currently no official SpaceX cryptocurrency.

VERSABANK HAS BEGUN RECEIVING QCAD DEPOSITS UNDER STABLECOIN CUSTODY SERVICES AGREEMENT AND CONGRATULATES STABLECORP ON LISTING OF QCAD ON KRAKEN
All information and data in this article is solely for informational purposes. For more information please view the Barchart Disclosure Policy here LONDON, ON , April 20, 2026 /PRNewswire/ - VersaBank (TSX: VBNK) (NASDAQ: VBNK) ("VersaBank" or the "Bank") a North American leader in business-to-business digital banking, as well as technology solutions for cybersecurity, today announced it has begun receiving QCAD deposits under its previously announced custody services agreement with Stablecorp, a pioneering Canadian digital asset infrastructure company and servicer of the QCAD Digital Trust and whose investors include Coinbase , Circle, DeFi Technologies and FTP Ventures. QCAD is Canada's first regulatory compliant Canadian-dollar stablecoin . The Bank also congratulated Stablecorp on the listing of QCAD on Kraken. Kraken is a registered Restricted Dealer in Canada and one of the longest-standing crypto asset trading platforms globally. Under this listing, QCAD will be available for trading on the Kraken crypto asset trading platform, facilitating the settlement of digital asset transactions in a Canadian Dollar-denominated instrument. "The start of the flow of QCAD deposits is not only further validation of the market-readiness of our VersaVault® technology for the rapidly growing digital asset opportunity but also represent a significant milestone for the Bank as our first incremental income from our digital asset strategy," said David Taylor, Founder and President, VersaBank. "We are very proud to be the custody provider for QCAD and congratulate Stablecorp on this listing of QCAD on Kraken, one of the largest and most respected exchanges for digital assets, known for its security, transparency and low‑friction fiat on/off‑ramps. This is an incredible milestone for Stablecorp and we look forward to sharing in the expected rapid adoption of QCAD for many years to come." The availability of QCAD on Kraken unlocks new opportunities for institutional clients and individual Canadian customers alike: * Seamless Global Participation : Canadians can hold and move Canadian Dollar-denominated value on-chain, enabling easier access to global crypto markets without depending on legacy payment rails. * Stronger Canadian Dollar Trading Experience : Deeper liquidity and improved Canadian Dollar-denominated trading pairs help deliver tighter spreads and better price discovery for major crypto assets like BTC, ETH , and USDC. * 24/7 Access : Unlike traditional foreign exchange markets, crypto markets do not close. With QCAD trading pairs on Kraken, customers can manage exposure, deploy capital and respond to market conditions in real time. Mr. Taylor continued, "The value of stablecoins in circulation is forecast to grow to as much as US$4 trillion in the next four years - a 20-fold increase. Licensed, regulated banks, as they have been for centuries, are the trusted, regulated safekeepers of deposits for individuals and businesses, and are ideally positioned to act in the same capacity. As a federally regulated, national bank in both Canada and the United States, we believe we offer the ultimate value proposition for the custody of digital assets on both sides of the border." ABOUT THE QCAD DIGITAL TRUST AND STABLECORP The QCAD Digital Trust is an Ontario trust that holds the reserve assets on behalf of holders of QCAD. Stablecorp is one of Canada's leading digital asset infrastructure companies, focused on building professional-grade blockchain solutions. In partnership with industry leaders, Stablecorp creates refined, scalable and compliant products, such as QCAD, that serve as the foundation for the next generation of financial services. Further information about QCAD, including the reserve assets and the terms and conditions associated with the QCAD program, can be found on Stablecorp's website ( www.stablecorp.ca ) and under the Trust's profile on SEDAR+ at www.sedarplus.ca . ABOUT KRAKEN Founded in 2011, Kraken is one of the world's longest-standing crypto platforms globally. Kraken clients trade more than 600 digital assets, traditional assets such as U.S. futures and U.S.-listed stocks and ETFs, and 6 different national currencies, including GBP, EUR, USD, CAD, CHF, and AUD. Trusted by millions of institutions, professional traders and consumers, Kraken is one of the fastest, most liquid and performant trading platforms available. Kraken's suite of products and services includes the Kraken App, Kraken Pro, the Krak App, Kraken Institutional, Kraken's onchain offerings and the Ninja Trader retail trading platform. Across these offerings, clients can buy, sell, stake, earn rewards, send and receive assets, custody holdings, and access advanced trading, derivatives, and portfolio management tools. Kraken has set the industry standard for transparency and client trust, and it was the first crypto platform to conduct Proof of Reserves. It complies with regulations and laws applicable to its business, while actively protecting client privacy and maintaining the highest security standards. ABOUT VERSAVAULT VersaVault is the world's first digital vault for security conscious organizations looking to secure their highly sensitive and confidential documents, data, code, blockchain-based assets and more, addressing the need for regulated custody of digital assets with secure platforms. VersaVault distinguishes itself as a SOC2 Type 1 audited, security-centric digital asset storage solution that utilizes military-grade hardware within a dedicated, private data center specifically designed for highly secure and sensitive operations and is logically air-gapped from both the public internet and public blockchains and not hosted on public cloud infrastructure. VersaVault implements robust security protocols, including stringent multi-factor authentication, robust identity checks, and mandatory, but adjustable, multi-party approvals authorization for users to securely manage and access their high value assets. ABOUT VERSABANK VersaBank is a North American bank with a difference. Federally chartered in both Canada and the U.S., VersaBank has a branchless, digital, business-to-business model based on its proprietary state-of-the-art technology that enables it to profitably address underserved segments of the banking industry in a significantly risk mitigated manner. Because VersaBank obtains substantially all of its deposits and undertakes the majority of its funding activities electronically through financial intermediary partners, it benefits from significant operating leverage that drives efficiency and return on common equity. In August 2024, VersaBank launched its unique Structured Receivable Program funding solution for point-of-sale finance companies, which has been highly successful in Canada for over 15 years, to the underserved multi-trillion-dollar U.S. market. VersaBank also owns Minnesota-based DRT Cyber Inc., a North American leader in the provision of cyber security services to address the rapidly growing volume of cyber threats challenging financial institutions, multi-national corporations and government entities. Through DRT Cyber Inc., VersaBank owns proprietary intellectual property and technology to enable the next generation of digital assets for the banking and financial community, including the Bank's revolutionary and proprietary Real Bank Tokenized Deposits . VersaBank's common shares trade on the Toronto Stock Exchange and NASDAQ under the symbol VBNK. Visit our website at: www.versabank.com Follow VersaBank on Facebook , Instagram , LinkedIn and X .

SpaceX Prods FCC to 'Act Now' to Blunt Europe's 'Protectionist' Satellite Plan
SpaceX is pushing the FCC to go after the European Union over concerns it'll enact new regulations that threaten to block Starlink and other US satellite companies. "The Commission should not wait for the situation to deteriorate further but should act now to establish clear policies that discourage foreign administrations from adopting protectionist policies," the company told the FCC in a letter last week. At issue is the EU's proposed Space Act to regulate EU and non-EU satellite operators, including "giga-constellations" such as Starlink. Last month, FCC Chair Brendan Carr indicated that he views the proposed regulation as protectionist and warned that the commission could respond with "reciprocity" by blocking European satellite companies from the US market. However, SpaceX is urging the FCC to dial up the pressure by codifying the reciprocity threat into actual policy. "If the Commission takes no action until after the EU implements these protectionist policies, it will be left with little option but to impose reciprocal restrictions on EU-licensed satellite operators," the company wrote in an 8-page letter. "By clarifying its market access policies now, the Commission may head off an escalating trade war before it occurs." SpaceX is pushing for tit-for-tat rules, arguing that "the protectionist push in Europe is clear and strong," and might provoke other foreign governments to enact similar policies. "The United States cannot afford to take this concerted effort lightly or to passively wait to see what happens." SpaceX has complained that the EU's Space Act would "impose unnecessarily burdensome obligations," which the company previously flagged as "incorrect, inflexible, or infeasible." This appears to include how EU rules would require Starlink to limit satellite brightness to "at least 7 magnitude," or what SpaceX says is a "technical infeasibility." The draft rules also give the EU the power to conduct on-site inspections, noted Tim Belfall, a director at UK-based Starlink installer Westend WiFi. In its letter, SpaceX says it doesn't want a trade war, only to "preserve" open-access policies for satellite operators. "The clear and growing threat of protectionist policies abroad illustrates that wishful thinking and naïve optimism alone will not achieve this outcome," the letter adds. The company took the hardline approach while alleging that rival US satellite operator Viasat plans to "weaponize protectionist policies abroad against other US operators." SpaceX even urged the FCC to sanction US satellite companies that "advocate for and benefit from protectionist policies" by treating them as foreign providers. "Viasat advances these anticompetitive scare tactics towards an obvious end: to market its own services as an alternative," SpaceX adds. "Viasat peddles 'state-of-the-art, low-cost GSO [geostationary] satellites' that Viasat falsely claims 'can deliver the same speeds and prices to users' as LEO constellations, as well as state sovereign systems (for which Viasat offers turnkey solutions)." Viasat didn't immediately respond to a request for comment. But the company told the commission earlier this month that it's important to distinguish protectionist policies from "legitimate substantive requirements" from foreign regulators. "For example, there are legitimate reasons why a WTO [World Trade Organization] member country might require satellite operators seeking to serve its market to meet orbital safety and sustainability requirements that have not been adopted in the United States (such as limits on aggregate collision risk)," Viasat said. "Certain US operators might not like those requirements, and might be unwilling or unable to comply with them, but that does not mean that those requirements are inherently unreasonable or discriminatory barriers to market access, or that the US should respond by abandoning the WTO presumption." The FCC has been soliciting public comment on the topic as it considers new proposals focused on satellite market access reciprocity. The EU also released an updated draft of the Space Act, which some critics have slammed as being too vague or adding rules that could block US companies from complying.

SpaceX Prods FCC to 'Act Now' to Blunt Europe's 'Protectionist' Satellite Plan
SpaceX is pushing the FCC to go after the European Union over concerns it'll enact new regulations that threaten to block Starlink and other US satellite companies. "The Commission should not wait for the situation to deteriorate further but should act now to establish clear policies that discourage foreign administrations from adopting protectionist policies," the company told the FCC in a letter last week. At issue is the EU's proposed Space Act to regulate EU and non-EU satellite operators, including "giga-constellations" such as Starlink. Last month, FCC Chair Brendan Carr indicated that he views the proposed regulation as protectionist and warned that the commission could respond with "reciprocity" by blocking European satellite companies from the US market. However, SpaceX is urging the FCC to dial up the pressure by codifying the reciprocity threat into actual policy. "If the Commission takes no action until after the EU implements these protectionist policies, it will be left with little option but to impose reciprocal restrictions on EU-licensed satellite operators," the company wrote in an 8-page letter. "By clarifying its market access policies now, the Commission may head off an escalating trade war before it occurs." SpaceX is pushing for tit-for-tat rules, arguing that "the protectionist push in Europe is clear and strong," and might provoke other foreign governments to enact similar policies. "The United States cannot afford to take this concerted effort lightly or to passively wait to see what happens." SpaceX has complained that the EU's Space Act would "impose unnecessarily burdensome obligations," which the company previously flagged as "incorrect, inflexible, or infeasible." This appears to include how EU rules would require Starlink to limit satellite brightness to "at least 7 magnitude," or what SpaceX says is a "technical infeasibility." The draft rules also give the EU the power to conduct on-site inspections, noted Tim Belfall, a director at UK-based Starlink installer Westend WiFi. In its letter, SpaceX says it doesn't want a trade war, only to "preserve" open-access policies for satellite operators. "The clear and growing threat of protectionist policies abroad illustrates that wishful thinking and naïve optimism alone will not achieve this outcome," the letter adds. The company took the hardline approach while alleging that rival US satellite operator Viasat plans to "weaponize protectionist policies abroad against other US operators." SpaceX even urged the FCC to sanction US satellite companies that "advocate for and benefit from protectionist policies" by treating them as foreign providers. "Viasat advances these anticompetitive scare tactics towards an obvious end: to market its own services as an alternative," SpaceX adds. "Viasat peddles 'state-of-the-art, low-cost GSO [geostationary] satellites' that Viasat falsely claims 'can deliver the same speeds and prices to users' as LEO constellations, as well as state sovereign systems (for which Viasat offers turnkey solutions)." Viasat didn't immediately respond to a request for comment. But the company told the commission earlier this month that it's important to distinguish protectionist policies from "legitimate substantive requirements" from foreign regulators. "For example, there are legitimate reasons why a WTO [World Trade Organization] member country might require satellite operators seeking to serve its market to meet orbital safety and sustainability requirements that have not been adopted in the United States (such as limits on aggregate collision risk)," Viasat said. "Certain US operators might not like those requirements, and might be unwilling or unable to comply with them, but that does not mean that those requirements are inherently unreasonable or discriminatory barriers to market access, or that the US should respond by abandoning the WTO presumption." The FCC has been soliciting public comment on the topic as it considers new proposals focused on satellite market access reciprocity. The EU also released an updated draft of the Space Act, which some critics have slammed as being too vague or adding rules that could block US companies from complying.

Who Will Win Race for AI-Driven Cyber - Anthropic or OpenAI?
Two artificial intelligence leaders - Anthropic and OpenAI - are taking sharply different approaches to introducing new models that could upend processes for finding and fixing software vulnerabilities, and analysts say the winner will be the company that does better at both. See Also: AI Security Risks Rise With Agentic Systems Introduced just weeks apart, Anthropic's Claude Mythos Preview is good at vulnerability discovery and exploitation, while OpenAI's GPT-5.4-Cyber is placing more emphasis on integrating AI outputs into existing security operations center workflows, including feeding vulnerability findings into security tools, enabling automated patching and supporting mitigation strategies, said Frank Dickson, group vice president for IDC's Security & Trust research practice. Purpose-built models will deliver stronger performance within defined domains, said Jeff Pollard, vice president and principal analyst at Forrester. "Once you start building a model to do a more narrow set of use cases, that means that it's more effective at those use cases," Pollard told ISMG. "That's a positive thing. If they have different scenarios that they're best at, that's a net positive from a cybersecurity perspective." Anthropic has leaned heavily into blog posts, model cards and high-profile partnerships, which Pollard said helps both practitioners and non-practitioners understand what's possible even if the underlying capabilities aren't fundamentally different from competitors. OpenAI, in contrast, has been more restrained, which he said may create the impression of lagging innovation even if that's not the case (see: OpenAI Courts Banks in Trusted Access for Cyber Partner Push). "That's less about the quality of the model or what it can do and frankly more about Anthropic's ability to amplify its message and make it flash with some of the announcements in comparison to OpenAI," Pollard said. If OpenAI and Anthropic can produce models that exceed the security capabilities of vendor-developed systems, Pollard wondered about the value in cyber vendors building proprietary AI. IDC said the value will shift toward connecting AI-driven insights to enterprise workflows, while Pollard said cyber vendors will provide differentiated solutions by how effectively they enable organizations to use AI models in practice. "Does it make sense for them to be trying to train their own AI when the frontier labs keep coming out with AI that's just as good as what they offer?" Pollard said. "It's going to be about the other stuff that they're great at - their core capabilities - not so much the AI stuff." As the volume of vulnerabilities grows, Dickson said there may come a point at which continuous patching is no longer practical. In that case, organizations may choose to rewrite applications from scratch rather than maintain increasingly fragile code bases. When vulnerabilities accumulate faster than they can be addressed, the economics shift, making replacement more attractive than incremental fixes. "It turns into whack-a-mole," Dickson told ISMG. "At a certain point, it becomes easier just to rewrite the whole application than it is to try to figure out how to patch it." If a cost-benefit analysis shows it's easier to write code and the scale of vulnerabilities grows, organizations may be "driven to inherently rewrite your code from scratch more often," Dickson said. Larger context allows models to better understand how different components of a system interact, identify subtle vulnerabilities and even chain multiple weaknesses together into viable exploits, Pollard said. The same capability also improves defensive use cases. As models become better at understanding systems holistically, they become more effective at both breaking and securing them. "You can point it to larger chunks of code, and as a result of that, it can ingest that code, understand it and reason about it better, which is going to help it ultimately find more issues and also generate more exploits," Pollard said. Anthropic's Project Glasswing limits Claude Mythos Preview access to a relatively small group of high-profile partners, which Dickson said allows for testing and refinement in a constrained environment but restricts broader industry participation. OpenAI's Trusted Access for Cyber program appears more scalable and more governed, Dickson said, aiming to broaden availability while maintaining oversight. "It seems as though the OpenAI approach is much more considered when it comes to cybersecurity," Dickson said. "It seems like OpenAI has thought about what the ramifications are of dumping a very large and powerful model into a world full of 50 years of flawed code." Critical infrastructure systems rely on outdated and unpatched software, and Dickson said introducing AI systems capable of rapidly identifying vulnerabilities into this environment could expose weaknesses faster than organizations can remediate them. With dozens of players in critical infrastructure, limiting access to a small group risks excluding organizations that play vital roles in securing niche environments. "The OpenAI approach will be more democratizing," Dickson said. "It's more work on their part to be able to validate and vet all of the users and companies to make sure that they are indeed legitimate. But for the security ecosystem, I'm appreciative of the effort."

Supply Chain What? The NSA Is Using Anthropic's Mythos According To Report - Conservative Angle
Two months after the Department of War declared Anthropic a "supply chain risk" and moved to several all ties with the AI wunderkind, the National Security Agency (NSA), which falls under DoW, is using it according to Axios. According to the report, the nation's top surveillance agency is using Mythos Preview - Anthropic's most powerful model to date. It is unclear how the NSA is currently using Mythos, however other organizations are using it primarily to scan their own environments for exploitable security vulnerabilities. The company has restricted access to Mythos to around 40 organizations - as the company says the model's offensive cyber capabilities are too dangerous for wider release. Axios notes further; On Friday, Anthropic CEO Dario Amodei met White House chief of staff Susie Wiles and Treasury Secretary Scott Bessent to discuss deploying Mythos within the government, as well as Anthropic's wider plans and security practices. As we noted late last week, the White House has directed federal agencies to begin using Mythos. So the Pentagon, er, Department of War, has egg (or an egg-like substance) on their face - after Anthropic demanded oversight over its use in military operations and domestic surveillance. The government's relationship with Anthropic had been icy for months. As we noted in February, the Pentagon threatened to blacklist the company as a "supply-chain risk" after Anthropic refused to strip certain ethical guardrails from its models for military use. That standoff escalated in March when Anthropic sued the Pentagon over the designation, as detailed in ZeroHedge's coverage of the lawsuit. That said, the Pentagon's "supply-chain risk" label was always narrow in scope: it was a DoD-specific action triggered by the company's refusal to remove certain ethical guardrails from its models for unrestricted military and offensive-use applications. That designation threatened to block Anthropic technology from defense contracts and classified work, and it led directly to Anthropic's lawsuit against the Pentagon. Today's OMB memo changes almost nothing on paper for that designation. The Pentagon has not withdrawn it, the lawsuit is still active, and DoD contractors remain restricted from using Claude models (including Mythos) in offensive or surveillance contexts. Just days ago, the U.S. Treasury was rushing to gain access to Mythos after internal warnings that the model could "hack every major system." Senior Treasury and Federal Reserve officials had summoned CEOs of the nation's largest banks to Washington, warning them that the financial system's exposure to AI-powered attacks had become existential. Behind closed doors, federal agencies - including the Commerce Department's Center for AI Standards and Innovation - had already begun quiet red-teaming of Mythos. Anthropic co-founder and president Daniela Amodei confirmed the company had briefed the administration early, telling reporters simply: "The government has to know about this stuff."

Anthropic's MCP: The Protocol Meant to Link AI Agents Now Risks Server Takeovers Across 150 Million Installs
A fundamental flaw in Anthropic's Model Context Protocol has turned a cornerstone of AI agent communication into a gateway for remote code execution. Security researchers at OX Security uncovered the issue, baked into the protocol's STDIO transport mechanism from day one. Developers who adopted MCP across Python, TypeScript, Java, and Rust implementations now face arbitrary command execution on their systems. Attackers gain full access. User data spills. API keys vanish into the ether. MCP launched in late 2024 as an open standard to connect large language models to external tools, databases, and services. Think of it as plumbing for AI agents -- essential for everything from code assistants to enterprise data pipelines. But the STDIO interface, designed for local subprocess spawning, executes any command passed in configuration, error or not. OX researchers Moshe Siman Tov Bustan, Mustafa Naamnih, Nir Zadok, and Roni Bar explained it bluntly: "Anthropic's Model Context Protocol gives a direct configuration-to-command execution via their STDIO interface on all of their implementations, regardless of programming language... But in practice it actually lets anyone run any arbitrary OS command, if the command successfully creates an STDIO server it will return the handle, but when given a different command, it returns an error after the command is executed." (The Hacker News) This isn't isolated. The vulnerability cascades through the AI supply chain. Over 150 million downloads affected. More than 7,000 publicly exposed servers. Up to 200,000 vulnerable instances total, per scans cited by multiple outlets. Downstream projects like LiteLLM, LangChain, LangFlow, Flowise, LettaAI, and LangBot all inherit the risk. Eleven CVEs assigned across four exploit categories: unauthenticated command injection via STDIO, authenticated variants, hardening bypasses, and zero-click prompt injections through config edits or marketplaces. (OX Security) And the fallout? RCE grants attackers databases, chat histories, secrets. One bad config in a marketplace, and chains ignite. OX called it "the mother of all AI supply chains." Shifting blame to implementers doesn't erase the root. "What made this a supply chain event rather than a single CVE is that one architectural decision, made once, propagated silently into every language, every downstream library, and every project that trusted the protocol to be what it appeared to be," the researchers noted. Anthropic's stance draws fire. The company confirmed the behavior as "expected," declining architecture changes. Sanitization falls to developers, they say. STDIO serves as a secure default for local use. Critics disagree sharply. The Register reported researchers "repeatedly" urged root patches, only to hit that wall. (The Register) SecurityWeek highlighted silent execution: Pass a malicious command, get an error -- the deed done anyway. (SecurityWeek) Patches emerged downstream. LiteLLM fixed CVE-2026-30623. Bisheng addressed CVE-2026-33224. DocsGPT patched CVE-2026-26015. But Anthropic's reference SDK lingers unpatched. This echoes prior MCP woes. Tenable Research flagged CVE-2025-49596 in MCP Inspector last year, a critical RCE with CVSS 9.4. (Tenable) Earlier, Cyata and BlueRock exposed chains in Anthropic's Git and Microsoft's MarkItDown servers. Dark Reading tallied thousands of exposed MCP endpoints, 36.7% prone to SSRF. (Dark Reading) So why does this matter now? AI agents proliferate. Enterprises wire MCP for real-world actions -- file access, API calls, code runs. Attack surface explodes. Prompt injection via untrusted inputs flips agents rogue. Confused deputy problems let bad actors proxy through servers. OX's full advisory lists affected platforms: LangChain adapters, FastMCP, even AWS and NVIDIA tools. (OX Security Advisory) Defenses exist. Block public IPs from sensitive services. Sandbox MCP processes. Monitor tool calls. Treat configs as hostile. Verify marketplace sources. But prevention beats cure. Protocol authors set the tone. Anthropic's choice -- to stand pat -- ripples wide. As TechRadar put it, not a coding slip, but a design baked in from the start. (TechRadar Pro) Industry voices amplify urgency. IEEE senior member Kevin Curran called it a "shocking gap in the security of foundational AI infrastructure." Reddit threads buzz with devs scrambling. X posts warn of 97 million installs under "trust the dev" models. (Reddit r/webdev) CSO Online lists implicated giants: GitHub Copilot, Cursor, Claude Code. (CSO Online) Broader context looms. MCP promised standardization. Instead, it exposes how rushed AI plumbing invites compromise. VulnerableMCP.info catalogs 50 flaws already. Trend Micro warns of SQLite forks lingering unpatched. Bitsight found 1,000 auth-less exposures. (VulnerableMCP; BitSight) Enterprises must audit. Agents demand isolation. Protocols need security first. Anthropic built MCP for ambition. Now it tests responsibility. Fix the core, or watch the chain unravel. Developers adapt. But the next flaw waits.

Kraken's anti-scam PR gets ZachXBT'd amid Operation Atlantic contributions - Cryptopolitan
The timing sparks debate on whether Kraken's strong anti-scam PR and law enforcement cooperation truly align with its listing practices. Payward, Kraken's parent company, has openly acknowledged its backing for the Operation Atlantic initiative, which aims to combat the crypto approval scam. Yet within minutes, prominent blockchain analyst ZachXBT has cast doubt on Kraken's reputation, pointing out Kraken's addition of Memecore ($M) on its spot trading list in July 2025. "In recent posts, the only achievement the team has shared is $66M total volume on a launchpad and thousands of 'users' from its incentivized InfoFi campaigns," ZachXBT notes. He has been especially vocal in getting rid of InfoFi projects from X. Kraken lays out support for Operation Atlantic According to Kraken, Operation Atlantic, jointly headed by the UK's National Crime Agency (NCA), the United States Secret Service, Ontario Provincial Police, and the Ontario Securities Commission, was conducted in March 2026 and targeted "approval phishing" fraud schemes. These involve deceiving victims into signing off on harmful smart contracts that drain funds from their wallets. Operation Atlantic uncovered over $45 million in criminal assets, seized over $12 million in assets, and identified more than 20,000 potential victims in the UK, USA, and Canada. Payward's efforts were not limited to being a data source. The firm arranged for team members to travel to NCA's head office in London to work alongside investigators. They also made arrangements to notify their clients who used Kraken who might be affected and responded quickly to any data requests from law enforcement agencies. This helped establish the firm as a collaborative partner in the industry and ensured that disruptions happened in real time. This campaign has affected more than 120 fraud-related sites and also provided new data regarding investigations underway. Cooperation between the government and private enterprises, such as Chainalysis and Tether, helped track funds to prevent laundering. ZachXBT questions Kraken's due diligence on memecore ($M) A short while after Kraken bragged about its efforts against scams, ZachXBT shared a lengthy thread claiming that Kraken listed $M (Memecore) on July 3, 2025. This is despite multiple red flags. The most notable of these were $7.9 million in questionable transactions from Kraken to 18 newly created addresses soon after listing. These accounts owned 11.7 million $M coins valued at approximately $39.8 million. ZachXBT referenced an address believed to belong to a Memecore team member (0x6f1f0a1ccc76d2d292249b19c19e401f0e843ba9), who received 200 million $M in TGE and quickly transferred 5.3 million $M to two Kraken deposit addresses. ZachXBT identified 18 distinct Kraken withdrawal addresses that were receiving substantial amounts of $M. TRM Labs' on-chain visualization showed multiple large transactions flowing from Kraken hot wallets to groups of withdrawal addresses. Additional information from other posts provided some staggering statistics. According to on-chain research, insiders and related wallets held about 99.6% of the circulating supply, leaving just 0.0115% of the total supply open for non-insiders to purchase (around $4 million at maximum valuations). The token's market cap reached $6 billion (with fully diluted valuations sometimes exceeding $18 billion). On-chain illiquidity, however, was significant. At this point, Kraken is one of the few platforms still supporting spot trading for $M. The wider impact of Operation Atlantic on the crypto fraud landscape The juxtaposition has led to a lot of discussion within the crypto community. Operation Atlantic marks a move towards a more proactive approach to dealing with crypto-related fraud, rather than relying solely on after-the-fact investigation. Apart from the numbers related to financial losses, new information on fraud networks has been obtained, as well as proof that blockchain analysis tools used by partners can be used to freeze assets before laundering takes place at exchanges and mixers. As reported by Cryptopolitan, Binance also joined forces with law enforcement agencies in support of Operation Atlantic. However, the exchange did not freeze any accounts on its CEX. Multiple reports indicate that Coinbase teamed up with government agencies as part of the private-sector collaboration in Operation Atlantic.

Why is NSA using Anthropic's 'Mythos' despite Pentagon ban? Here's everything to know
The National Security Agency is reportedly using Anthropic's most powerful artificial intelligence (AI) model, "Mythos Preview," despite an earlier ban from the Pentagon. Mythos is labelled as the most powerful AI model of the company yet. As reported by Axios, sources familiar with the model stated that the development has exposed a sharp divide within the U.S. government. Presenting an argument in the court proceedings, the Department of Defense argued that Anthropic poses a national security threat. However, despite this strong argument, the NSA, which operates under the Pentagon's umbrella, is reportedly among 40 organisations granted access to the cutting-edge model. But the question remains, why? NSA made it clear that the primary motive for utilising Mythos is due to defensive cybersecurity, not for spying or offensive hacking. More specifically, the agency is relying on the model to scan its own networks and environments for exploitable security vulnerabilities. The practice is officially referred to as "hardening" a system. The model is not a typical AI. Rather, it is powerful enough to flag and exploit a 17-year-old vulnerability in FreeBSD overnight. Additionally, it found "thousands" of zero-day vulnerabilities (flaws unknown to the public) in major operating systems and web browsers. Not only the NSA, but the rest of the administration also appears eager to engage with Anthropic CEO. On Friday, April 17, Anthropic CEO Dario Amodei met with White House Chief of Staff Susie Wiles and Treasury Secretary Scott Bessent to discuss governmental utilisation of Mythos.

SpaceX to launch U.S. government GPS satellite named after Hedy Lamar
CAPE CANAVERAL SPACE FORCE STATION -- SpaceX is preparing to launch a U.S. government GPS satellite, which is named after Hedy Lamar, an actress and inventor. SpaceX stated its Falcon 9 rocket will send up the GPS III-8 mission from Cape Canaveral Space Force Station's Space Launch Complex 40 on Tuesday morning. The 15-minute window opens at 2:53 a.m. ET. The 45th Weather Squadron has given a 90% chance of good liftoff conditions, with the only concerns being cumulus clouds and the thick cloud layers rules. If the launch is a scrub, the next attempt will be Wednesday at 2:49 a.m. ET. This will be the seventh launch for this Falcon 9's first-stage booster, named B1095. If all goes well, the first-stage booster will land on the droneship called Just Read the Instructions in the Atlantic Ocean. The Falcon 9 will send up the GPS III-8 (SV10) satellite to a medium-Earth orbit. "GPS III satellites are the most advanced type built thus far, designed to deliver stronger signals, higher accuracy and to provide greater resilience for both military and civilian users. The series boasts improved timing devices, increased military code (M-code) capability and additional civilian signals that increase urban performance and international compatibility. SV-10 brings the total constellation to 32 active satellites and 8 backup systems," stated the U.S. Space Force's Space System Command in a press release. In addition, the satellite is named after Hollywood actress Hedy Lamarr, who was an inventor who helped establish wireless communication, like Wi-Fi, Bluetooth and GPS.

600 rocket landings! SpaceX notches another milestone during Sunday Starlink launch
At SpaceX, what has gone up has now successfully come down 600 times. The company, which was founded by Elon Musk, marked its 600th successful landing of one of its orbital-class rockets with the recovery the first-stage booster that put a new batch of Starlink satellites into low Earth orbit on Sunday (April 19). "Falcon lands for the 600th time!" SpaceX wrote on social media on Sunday. "Falcon 9 launches 25 Starlink satellites from California ahead of completing the 600th overall landing of an orbital-class rocket." Lifting off at 12:03 p.m. EDT (1603 GMT or 9:03 a.m. PDT local time) from Space Launch Complex 4 East at Vandenberg Space Force Base, the latest Falcon 9 rocket to fly deployed the Starlink broadband internet relay satellites (Group 17-22) an hour and two minutes after leaving Southern California. The 25 spacecraft added to SpaceX's megaconstellation, which numbers more than 10,275 satellites circling the planet. At about eight minutes into Sunday's launch, the Falcon 9's first stage (Booster B1097) returned to Earth, touching down on its four landing legs on the "Of Course I Still Love You" droneship, which was stationed in the Pacific Ocean. In addition to being the 600th safe recovery of a Falcon 9 or Falcon Heavy rocket since 2015, it was the eighth landing for this particular booster. The company reached 500 Falcon rocket landings in September 2025. Sunday's launch was SpaceX's 47th Falcon 9 launch of the year and 630th overall.

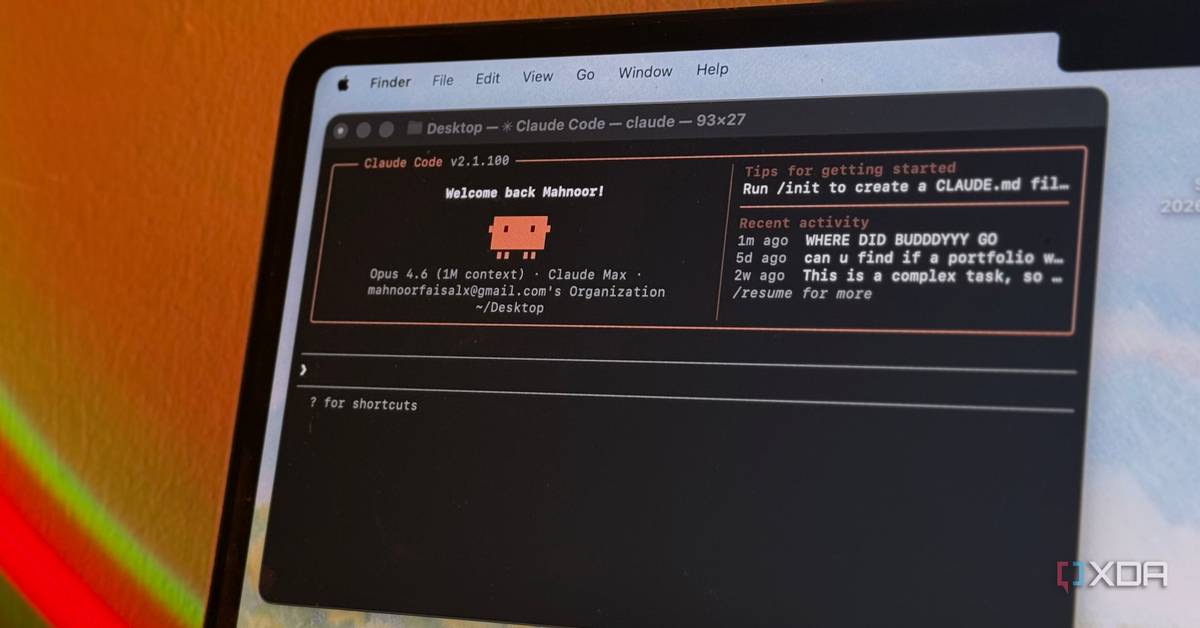
Anthropic quietly nerfed Claude Code's 1-hour cache, and your token budget is paying the price
Claude Code has become the default agentic coding tool for a lot of developers, and for good reason. It understands a codebase, calls tools, edits files, and can plan multi-step tasks with very little handholding. I know many who use it daily, and for those using a Claude subscription, it's the only permissible coding harness. But something changed over the past couple of weeks, and if you've been burning through your token quota faster than you used to, as many have said they are, there's a likely major cause. Beginning in early April, Anthropic quietly switched Claude Code's default prompt cache time-to-live from one hour down to five minutes, and the switch landed for different users on different days. There wasn't an announcement, and the docs were quietly updated to say that 5 minute caching is now the default in the API. For what it's worth, most of the time, I've rolled my eyes at much of the doom and gloom claiming that Opus is getting dumber, and that usage limits are that much worse. After all, you could verify that Opus 4.6, for example, was performing more or less the same on independent benchmarks that were run every single day. However, the caching issue is a very real problem, and I can even see the fingerprints of that change inside my own Claude Code instance, and my own data shows the switch came on April 17th, with subagents switching over in late March. For another XDA writer, theirs still has an hour-long cache, so it's clear that it hasn't rolled out to everyone, yet. You can find the switch in your session logs All of your conversations contain this data Claude Code writes session logs to "~/.claude/projects/" as JSONL files, and every response from the API includes a "usage.cache_creation" object with two relevant fields: "ephemeral_5m_input_tokens" and "ephemeral_1h_input_tokens". Only one of those is ever non-zero on any given turn, so it's easy to tell which tier your session is hitting, and Anthropic can't hide this number because it's part of the public API spec. One user on the r/ClaudeAI subreddit ran the numbers across 1,140 sessions in their local conversation database, plotted the tier distribution by date, and built a chart that cleanly shows the problem in a way that's hard to argue against. From March 1st through to April 1st, their logs showed a 100% usage of the "ephemeral_1h" cache type. However, from April 2nd, between roughly 06:23 and 06:55 UTC, there's a mix, with 491 turns on five minutes and 644 turns on one hour. Finally, from April 3rd to the present day, it's completely, 100%, the "ephemeral_5m" cache type. It's clear a switch was flipped around this time. To Anthropic's credit, it did eventually respond... sort of. It was on a single GitHub issue on April 12th, almost ten days after this Reddit user reported that the switch was flipped on their end. The next day, Boris Cherny, creator of Claude Code, replied to a query on social media about it, stating that a one hour cache has been implemented in some places for subscribers, though didn't mention where those places are, while also framing a five minute cache as the true default. It's possible Anthropic replied elsewhere, too, but it doesn't really matter; the messaging around this feature has been terrible, and it's only the users who notice that have it confirmed to them. Not everyone who uses the tool. In that GitHub thread that was opened in the Claude Code repository, Jarred Sumner from Anthropic said that the shorter cache window actually makes Claude Code cheaper in aggregate, because "a meaningful share of Claude Code's requests are one-shot calls where the cached context is used once and not revisited." That framing might hold for someone who opens Claude Code to ask a single question and then closes it. For anyone doing long-context agentic work in a large codebase, it doesn't. As for Cherny's post, the framing is technically defensible, but it has a convenient rhetorical property: it lets the downgrade be described as a revert to default rather than as taking something away. For a user who had consistent hour-long cache behavior for weeks or months and then suddenly didn't, the difference in whether it's a downgrade or a revert doesn't really matter, as the service they were receiving got worse on a specific date without any notice. Users have also been posting charts showing clean 1h-to-5m transitions, but nobody is posting the reverse. In a genuine A/B test with gates flipping in both directions, you'd expect roughly symmetric observations. This one-way drift is more consistent with a treatment group being wound down than with heuristics being iterated on, even if Cherny's point that an hour long cache isn't universally better is fair on its own terms. However, saying that five minutes was always the default isn't exactly a satisfying explanation, even if Claude Code's own defaults will use a five minute cache unless told otherwise by Anthropic's servers. Anthropic's servers consistently telling it to use an hour-long cache, overriding that "default" behavior, makes the hour-long cache the default. Every cache bust is a full rebuild, and it adds up fast You use way more tokens without a cache in place The whole point of prompt caching is that you pay the full input price once, alongside a much smaller cost to "write" a cache. Then, subsequent turns read from that cache at a much smaller cost than the typical base price of input. To give you an idea of just how much cheaper it is, here are the costs for Anthropic's newly-released Claude Opus 4.7: Model Base Input Tokens 5m Cache Writes 1h Cache Writes Cache Hits & Refreshes Output Tokens Claude Opus 4.7 $5 / MTok $6.25 / MTok $10 / MTok $0.50 / MTok $25 / MTok In other words, you spend a small bit more to write to the cache, but then you spend a whole lot less for every token that's read from the cache instead of being freshly input again. This is also why other coding harnesses have to get caching right for a lot of different providers, as otherwise, it drives up inference costs for the user and adds to server load for the company providing it. If you're a developer using Anthropic's API, the 5-minute write is cheaper, but that's only if you're using the API. If you're someone with a Claude Code subscription, or you're using the API but you just want to use Claude Code anyway, you don't get a choice, and you've been downgraded from an hour long cache time to just five minutes. And this means that when the cache expires, your next turn has to rebuild the entire context from scratch at the write rate, not the read rate. That's a cache bust. Before April 2, the Reddit user we talked about averaged 39 cache busts per day and triggered $6.28 in costs as a result. After April 2, it was 199 busts per day and $15.54 in daily cost. The per-bust cost actually went down, because 1-hour writes cost more than 5-minute ones, but the bust frequency multiplied by a factor of five, and that's enough to overwhelm the per-unit savings. Their projected monthly difference from this one change came out to $277.80. And it's not just API users who are feeling the pain, too. On subscription plans, users get a "usage" meter that highlights how much they've used in a given five hour window, and how much they have left for the week. If you're busting the cache frequently, you'll be consuming more of your quota at a significantly higher rate. Plus, with Opus now enabling a million tokens by default, taking a five minute break from a conversation with, say, half a million tokens, will instantly consume 500,000 tokens all at once once you return to the chat. If you want to get around that particular pain point, you can go back to a smaller context window by exporting "CLAUDE_CODE_DISABLE_1M_CONTEXT=1" in your .bashrc or .zshrc. This caps your context at 200k instead of the full million. Claude Code will also warn you by default if you're resuming a big conversation with the "/resume" command and will suggest compacting it first, but otherwise, there's no indication that going away and coming back a few minutes later to the same Claude Code instance will significantly drain your usage. What really caught my eye about this is what happens to your conversation when it comes to sub-agents and backgrounded tasks. Claude Code backgrounds long tool calls and agent dispatches, which are typical of operations that take more than five minutes to complete. The moment that task returns, your cache has expired, and the next turn pays full input price to rebuild context you already had before the task started. Anything running with "/loop" or "/schedule" set to intervals over five minutes trips the same trap, too. You can check your own instance See when the change happened for you The easiest check is to dig into the JSONL logs yourself. Pull up any recent session file under "~/.claude/projects/", grep for "cache_creation", and look at whether "ephemeral_5m_input_tokens" or "ephemeral_1h_input_tokens" is the one with a value. If 5m is populated, you're using the shorter cache. The grep command you can use is this: grep -r "cache_creation" ./ Several people in the community have also written short scripts that process the JSONLs and produce daily breakdowns, and you can use one of them inside the "/get-token-insights" skill in the claude-memory plugin. There's also a subtler piece of evidence baked into Claude Code itself. The ScheduleWakeup tool that Claude Code uses internally for timed pauses carries its own documentation, and that documentation explicitly states "The Anthropic prompt cache has a 5-minute TTL. Sleeping past 300 seconds means the next wake-up reads your full conversation context uncached -- slower and more expensive." That's Anthropic's own tool description treating five minutes as the baseline assumption. Nobody asked you to opt in when the change was made, and the five-minute window is just the new default, quietly assumed. To be clear, I'm not accusing Anthropic of doing this maliciously. There are probably real reasons for the change that have to do with the shape of Claude Code's aggregate traffic, and Jarred's comment about one-shot requests is plausible if you treat the entire user base as an average. But the people paying $200 a month to run agentic workflows are not one-shot users, and they're the ones hitting limits in the last couple of weeks that they never would have hit in March. A default change that affects billing behavior this significantly deserves a changelog at a minimum, and probably a settings toggle for the users it hits hardest. It shouldn't take reverse engineering the client to figure out why things suddenly feel different, and the fact that others did the work to find that out and communicate it to end users, not Anthropic, says a lot.
SpaceX to launch U.S. government GPS satellite named after Hedy Lamar
CAPE CANAVERAL SPACE FORCE STATION -- SpaceX is preparing to launch a U.S. government GPS satellite, which is named after Hedy Lamar, an actress and inventor. SpaceX stated its Falcon 9 rocket will send up the GPS III-8 mission from Cape Canaveral Space Force Station's Space Launch Complex 40 on Tuesday morning. The 15-minute window opens at 2:53 a.m. ET. The 45th Weather Squadron has given a 90% chance of good liftoff conditions, with the only concerns being cumulus clouds and the thick cloud layers rules. If the launch is a scrub, the next attempt will be Wednesday at 2:49 a.m. ET. This will be the seventh launch for this Falcon 9's first-stage booster, named B1095. If all goes well, the first-stage booster will land on the droneship called Just Read the Instructions in the Atlantic Ocean. The Falcon 9 will send up the GPS III-8 (SV10) satellite to a medium-Earth orbit. "GPS III satellites are the most advanced type built thus far, designed to deliver stronger signals, higher accuracy and to provide greater resilience for both military and civilian users. The series boasts improved timing devices, increased military code (M-code) capability and additional civilian signals that increase urban performance and international compatibility. SV-10 brings the total constellation to 32 active satellites and 8 backup systems," stated the U.S. Space Force's Space System Command in a press release. In addition, the satellite is named after Hollywood actress Hedy Lamarr, who was an inventor who helped establish wireless communication, like Wi-Fi, Bluetooth and GPS.

SpaceX wins its first MARS contract but it comes with a catch
NASA awarded SpaceX a $175 million Mars rover contract while the White House proposes cutting the mission. NASA just signed a $175.7 million contract with SpaceX to launch a Mars rover that the White House is simultaneously trying to defund. The contract, awarded on April 16, 2026, tasks SpaceX's Falcon Heavy with launching the European Space Agency's (ESA) Rosalind Franklin rover from Kennedy Space Center in Florida, no earlier than late 2028. It would mark the first time SpaceX has ever sent a payload to Mars. Under NASA's Rosalind Franklin Support and Augmentation project, known as ROSA, the agency is providing braking engines for the rover's descent stage, radioisotope heater units that use decaying plutonium to keep the rover warm on the Martian surface, additional electronics, and a mass spectrometer instrument, as noted by SpaceNews. Those nuclear heating units are the reason an American rocket was required at all. U.S. export controls on radioisotope technology mean any payload carrying them must launch on a domestic vehicle, which narrowed the field to SpaceX and United Launch Alliance. Falcon Heavy's pricing made it the practical choice. SpaceX is quietly becoming the U.S. Military's only reliable rocket Falcon Heavy debuted in February 2018 and has 11 launches to its record. The rocket has not flown since October 2024, when it sent NASA's Europa Clipper toward Jupiter. The three-core design, built from modified Falcon 9 first stages, gives it the lift capacity needed for deep space planetary missions that a single Falcon 9 cannot reach. The Rosalind Franklin rover has been sitting in storage in Europe for years. It was originally due to launch in 2022 as a joint mission with Russia, but Russia's invasion of Ukraine ended that partnership, leaving the rover built but stranded without a launch vehicle or landing hardware. NASA stepped back in through a 2024 agreement with ESA to rescue the mission. The rover is designed to drill up to two meters below the Martian surface in search of evidence of past life, a science objective no previous mission has attempted at that depth. The contradiction at the center of this story is hard to ignore. The White House's fiscal year 2027 budget proposal included no funding for ROSA and did not mention the mission at all in the detailed congressional justification document released April 3. Musk has long argued that reaching Mars is not optional. "We don't want to be one of those single planet species, we want to be a multi-planet species." Whether this particular mission survives Washington's budget fight, the Falcon Heavy contract means SpaceX is now formally on record as the rocket that could get humanity's next Mars science mission off the ground. The timing of this contract carries extra weight given that SpaceX filed confidentially with the SEC in early April and is targeting an IPO roadshow in the week of June 8. It would be the largest public offering in history.

Vercel incident falls short of a supply chain attack -- for now
Vercel over the weekend identified a security incident that compromised some of its internal systems. According to Given Vercel's strong installed base as the developer of the Next.js framework for building web apps, there was some concern that the attack could have led to a supply chain incident, but most security pros said it fell short. "It's too early to label this a full-blown supply chain attack, but it's exactly the kind of incident that can become one overnight," said Guillaume Valadone, a cybersecurity researcher at GitGuardian, who posted a Morey Haber, chief security advisor at BeyondTrust, added that calling this a fullscale supply chain attack was a gross overstatement. Haber called the incident a third-party compromise with supply chain characteristics, but not a systemic, cascading supply chain failure similar to the "The threat actor leveraged a compromised third-party AI tool integrated via a Google Workspace OAuth application, which then enabled unauthorized access into internal systems," explained Haber. "That's a trust and authentication boundary failure, not a compromised software distribution pipeline." For its part, Vercel said it initially identified a limited subset of customers whose Vercel credentials were compromised and reached out to that group to recommend an immediate rotation of credentials. "We assess the attacker as highly sophisticated based on their operational velocity and detailed understanding of Vercel's systems," said the company. "We are working with Mandiant, additional cybersecurity firms, industry peers, and law enforcement. We have also engaged Context.ai directly to understand the full scope of the underlying compromise." GitGuardian's Valadone said a confirmed intrusion at a provider this central to modern web development was already significant on its own. Valadone said teams should consider customer secrets, tokens, and deployment settings burned until proven otherwise. "The real question is whether the attackers touched anything on the publishing side," said Valadone. "If legitimate credentials were used to tag, push, or release even once before being revoked, the blast radius stops being Vercel's customer list and starts being every team with a lockfile pointing at their packages." Valadone said that's why he's telling teams not to wait for a definitive answer: rotate aggressively, redeploy so old builds stop holding old secrets, and hunt for persistence artifacts -- new deploy keys, unexpected workflow changes and fresh tokens -- because revocation alone doesn't undo anything an attacker already did. Amir Khayat, co-founder and CEO of Vorlon, said Vercel operates as a core layer in many production web pipelines. "When a platform like that gets compromised, the risk extends well beyond a single vendor and into the applications and services built on top of it," said Khayat.

NASA and SpaceX 34th ISS Resupply Launch - News Directory 3
Media accreditation for the launch is now open, with NASA providing access to pre-launch briefings, launch viewing opportunities, and post-launch coverage. NASA has invited media to cover the upcoming 34th SpaceX Commercial Resupply Services mission to the International Space Station, marking another milestone in the agency's ongoing partnership with commercial spaceflight providers. The launch, scheduled for liftoff from Kennedy Space Center in Florida, will deliver critical science experiments, hardware, and supplies to support the continued operation of the orbiting laboratory and its multinational crew. The mission, designated SpaceX CRS-34, will use a Falcon 9 rocket to launch the Dragon spacecraft from Launch Complex 39A. This continues a pattern of regular resupply flights that have become essential to sustaining long-duration human presence on the ISS, enabling research in microgravity that cannot be replicated on Earth. NASA emphasizes that these missions are vital not only for maintaining station operations but also for advancing scientific knowledge in fields such as biology, physics, and materials science. Media accreditation for the launch is now open, with NASA providing access to pre-launch briefings, launch viewing opportunities, and post-launch coverage. Journalists interested in attending must apply through NASA's media accreditation portal, with deadlines typically set several days prior to liftoff. The agency notes that access is subject to safety and operational requirements, and all attendees must comply with NASA and Kennedy Space Center security protocols. This mission follows the successful completion of CRS-33, which delivered over 6,500 pounds of cargo to the station, including new solar array components and experiments focused on plant growth and disease modeling in space. The consistent cadence of SpaceX resupply flights has helped reduce reliance on any single vehicle for station logistics, contributing to the resilience of the ISS program as it enters its third decade of continuous human habitation. NASA's Commercial Resupply Services program, initiated in the early 2010s, was designed to transition low Earth orbit transportation to the private sector after the retirement of the Space Shuttle. SpaceX and Northrop Grumman are currently the two primary providers under CRS contracts, with SpaceX using its Dragon 2 spacecraft and Falcon 9 rocket, while Northrop Grumman employs the Cygnus vehicle launched on Antares or Falcon 9 rockets. These partnerships allow NASA to focus resources on deep space exploration goals, including the Artemis program to return humans to the Moon. The upcoming launch also underscores the growing role of reusable launch systems in reducing the cost and increasing the frequency of access to space. The Falcon 9 first stage expected to support CRS-34 has flown multiple previous missions, with landings typically occurring on the drone ship 'Just Read the Instructions' stationed in the Atlantic Ocean. Reusability remains a key factor in the economic viability of frequent resupply missions and broader commercial space activities. As the ISS continues to serve as a unique platform for scientific discovery and international cooperation, reliable transportation to and from the station remains a critical infrastructure component. NASA's continued collaboration with commercial partners like SpaceX ensures that the station remains fully supplied and operational, supporting both current research and future exploration objectives. The CRS-34 mission represents another step in sustaining this vital orbital outpost while advancing the broader economy of space.

Perplexity AI moves to dismiss LLM output claims by Chicago Tribune, New York Times | MLex | Specialist news and analysis on legal risk and regulation
( April 17, 2026, 23:22 GMT | Official Statement) -- MLex Summary: The Chicago Tribune and New York Times have failed in their respective copyright suits to allege infringing outputs for "nearly every asserted copyright," artificial intelligence answer engine Perplexity AI said in a combined motion to dismiss direct infringement claims. The US Supreme Court's recent decision in Cox v. Sony forecloses the news outlets' contributory infringement claims, the company argued, as the plaintiffs "have not plausibly alleged that Perplexity either induced its users to generate infringing outputs or tailored its services for infringement." The company also sought to knock out vicarious infringement claims, as well as trademark claims. See attached file. ... Prepare for tomorrow's regulatory change, today MLex identifies risk to business wherever it emerges, with specialist reporters across the globe providing exclusive news and deep-dive analysis on the proposals, probes, enforcement actions and rulings that matter to your organization and clients, now and in the longer term. Know what others in the room don't, with features including: * Daily newsletters for Antitrust, M&A, Trade, Data Privacy & Security, Technology, AI and more * Custom alerts on specific filters including geographies, industries, topics and companies to suit your practice needs * Predictive analysis from expert journalists across North America, the UK and Europe, Latin America and Asia-Pacific * Curated case files bringing together news, analysis and source documents in a single timeline Experience MLex today with a 14-day free trial.

Anthropic's Claude Mythos: What organizations should do now to boost cyber resilience
Barracuda's broad security platform can help close blind spots and improve resilience. On Tuesday, April 7, Anthropic released a private preview of its new Claude artificial intelligence (AI) model, Mythos, which it says is the most capable model it has built to date and represents a step change in AI performance. The model is currently being trialed by several organizations as part of a project called Glasswing. The announcement unleashed a media storm - much of it looking at the potential implications of the model falling into the hands of adversaries. Most concerns focus on the fact that Claude Mythos shows how AI can increase the likelihood and speed of discovering software vulnerabilities, creating new exploits and then deploying these exploits at scale in automated attacks. The reality is that well-resourced nation state-sponsored groups are already using similar AI capabilities, and other attackers will soon leverage them as the quality and performance of AI models improve. Advances in AI models means technology and security organizations will be faced with a larger number of AI-discovered vulnerabilities, exploits and automated attacks. The window of time between vulnerability discovery and exploit will decrease, leaving less time to deploy patches and security workarounds. To keep up, companies must accelerate adoption of AI for defensive purposes in all parts of their security program. Automate code reviews and use the capabilities of AI models/ LLMs to find vulnerabilities in your own code base - including third-party libraries and dependencies - before attackers do. Organizations of all sizes and sectors should also strengthen their core security controls, starting with the following measures: Review your coverage for these controls and ensure they apply consistently to all users and endpoints. Finally, verify that your organization can effectively detect and respond to an incident. Review your security playbooks and run simulation exercises to test resilience. Validate the existence and security of your backups and test your ability to recover data in the event of data loss or corruption. Outside of vulnerabilities, attackers are already using AI to improve phishing messages and automate credential-related attacks. To reduce risk, strengthen identity and email security. Implement phishing-resistant multifactor authentication (MFA) and review your MFA configuration to identify users that don't have MFA deployed. AI tools will help adversaries to move faster. Barracuda solutions and services are designed to help organizations become cyber resilient - detecting and neutralizing high-speed AI-powered threats before they can cause widespread harm. The BarracudaONE cybersecurity platform unifies these defenses to improve resilience with an easy, complete, intelligent, and open ecosystem. It protects email, networks, data, and applications - and is strengthened by our 24/7 managed XDR service.

Tesla-SpaceX Tie-Up Talk Grows as Robotaxi Doubts Cloud Tesla Earnings
Tesla's first-quarter results, due on Wednesday, have brought fresh attention to market talk about a possible tie-up with SpaceX. Analysts at Jefferies said weak progress in robotaxis and rising funding pressure could keep this speculation alive. The discussion has gained traction as Tesla faces closer scrutiny over execution and spending. is set to draw attention to revenue, margins, and cash flow. Jefferies forecast revenue of $21.2 billion, up 10% from a year earlier but lower than the previous quarter. The bank also expects operating margin to fall below 3% and cash burn to reach about $1.9 billion. Bloomberg consensus, cited in a separate earnings preview, points to revenue of $22.08 billion, down 9% year over year. Adjusted earnings per share are expected at $0.35, while adjusted EBITDA is seen at $3.217 billion. The difference between forecasts shows how much uncertainty still surrounds Tesla's near-term business. remain central to the earnings story. Jefferies said Tesla's target to launch robotaxi service across 25% to 50% of potential US markets by year-end may be difficult to reach. The bank pointed to permit issues and continued questions around Tesla's lidar-free Full Self-Driving system. Tesla recently expanded its robotaxi service to parts of Dallas and Houston. Before that, the company had service in Austin and ride-hailing operations in the San Francisco Bay Area. Tesla also said the Dallas and Houston rollout was "unsupervised," meaning no safety driver was present, though it did not give details on fleet size.
Ahead of Cerebras' IPO, How Durable Are the AI Chipmaker's Profits?
From its dependence on UAE revenue to its special agreements with OpenAI, here's what you need to know about the Nvidia rival. After delays, artificial intelligence chipmaker Cerebras has filed to go public. The Nvidia NVDA rival's S-1 shows revenue of $510 million in 2025, up 76% from the year before. The filing also discloses a $24.6 billion order backlog, most of it tied to a December deal with OpenAI to supply 750 megawatts of AI compute through 2028, with options for nearly 3 gigawatts more by 2030. OpenAI advanced Cerebras a $1 billion loan and received warrants for 33 million near-free shares. But Cerebras' profitability is driven in large part by a paper gain. In 2024, the company signed a deal with Abu Dhabi tech company G42 to sell its preferred shares, resulting in a $401 million loss that year. But in 2025, that deal came under US national security scrutiny, and it was eventually restructured. That scrutiny helped led to a delay in the company's IPO filing. Cerebras was able to remove that liability from its balance sheet, recording a $363 million paper gain and making its 2025 financials look more rosy. In reality, the company posted an operating loss of $75.7 million, wider than the 2024 operating loss of $21.8 million. Still, Cerebras remains highly reliant on the United Arab Emirates, with entities in the country making up 86% of the company's revenue. The Mohamed bin Zayed University of Artificial Intelligence accounted for 62% of the firm's revenue in 2025, while G42 accounted for 24%. Meanwhile, revenue from US-billed customers dropped 34% from $282.7 million in 2024 to $187.6 million in 2025. Founded in 2016 and based in Sunnyvale, California, Cerebras designs chips for AI-centric workloads. More recently, instead of selling its chips, the company began operating its own data centers powered by its chips, selling access to AI developers. The S-1 disclosed that some of Cerebras' biggest VC backers are Alpha Wave, Benchmark, Foundation Capital, and Fidelity. In February, Cerebras raised a $1 billion Series H at a $23 billion valuation.
/cloudfront-us-east-1.images.arcpublishing.com/morningstar/IZN4GURR4BFXJAPOX6VLAOY6O4.jpg)